Set up an iOS or iPadOS device in Shared Device Mode
Set up an iOS or iPadOS device in Shared Device Mode
Shared mobile devices are widely used across many industries, including manufacturing and retail. IDmelon Authenticator can be configured in shared device mode, enabling users to use their badge or biometric authentication to load passkeys into the device instantly. This allows users to access multiple applications with auto-login. The session time-to-live can be configured to support various shift change use cases with auto logout.
IDmelon Authenticator Shared Configuration Mode Features:
- Passkeys Autofill: Provides passkeys to the operating system for authentication.
- SSO Integration: Enables quick access to IDmelon-connected service providers.
- MSAL Integration: Streamlines access to Microsoft apps.
This configuration is tested with Microsoft Intune as MDM but can work with other MDMs as well to push configuration.
Prerequisites
- iOS or iPadOS 17 or later.
Configure IDmelon Authenticator
Use these managed app configuration keys to set up IDmelon Authenticator in shared device mode via your MDM (e.g., Microsoft Intune, Jamf, Kandji, VMware Workspace ONE). Push them as standard managed app settings to enrolled devices.
Scope: Controls shared-mode behavior, PIN prompts, self-service flows, shortcuts, and optional MSAL shared-mode integration.
Configuration Keys
| Key | Type | Required | Purpose |
|---|---|---|---|
shared_device_passkeys | Boolean | Yes | Enable shared device mode (true). |
authentication_type | String | Yes | When to prompt for PIN (onInit, onUse, none). |
device_id | String | Yes | MDM device identifier (e.g., Intune {{deviceid}}). |
api_key | String | Recommended | Auto-activate app (Admin Panel → Shared Mobile API key). |
one_time_use_passkeys | Boolean | No | Remove/invalidate passkey after first successful login. |
base_api_url | String | No | Target dedicated/on-prem API endpoint. |
self_service_url | String | No | Redirect to self-service enrollment if card isn’t registered. |
auto_logout | String | No | Scheduled logout (one-time use, 5m, 60m, 2h, 4h, 6h, 8h). |
shortcut_list | JSON string | No | In-app shortcuts (titles, URLs, icons). |
use_msal | Boolean | No | MSAL shared device mode flag (requires MS Authenticator shared mode). |
azure_client_id | String | No | Azure App Registration Client ID for MSAL. |
microsoft_sp_name | String | No | Microsoft’s service provider name (SSO) |
default_sp_for_auto_login | String | No | Set a service provider to log in automatically after the user signs in (SSO) |
open_url_after_login | String | No | Launches a specified app or URL immediately after the user signs in. |
open_url_after_logout | String | No | Launches a specified app or URL immediately after the user logs out. |
Key Details & Valid Values
shared_device_passkeys (Boolean, Required)
Enable shared device mode.
"shared_device_passkeys": true
authentication_type (String, Required)
Controls PIN prompts:
onInit— PIN once after first taponUse— PIN every loginnone— PINless login
"authentication_type": "onInit"
device_id (String, Required)
MDM device identifier used for device binding.
- Intune:
{{deviceid}} - Others: use the provider’s device identifier token
"device_id": "{{deviceid}}"
api_key (String, Recommended)
Auto-activates the app on first run (no manual activation). Generate under Admin Panel → Authentication → API Key Management → Create → Type: Shared Mobile.
"api_key": "YOUR_GENERATED_KEY"
one_time_use_passkeys (Boolean, Optional)
Logs user out after the first successful login with the passkey.
"one_time_use_passkeys": true
base_api_url (String, Optional)
Specify this when pointing to a dedicated/on-premises API endpoint.
"base_api_url": "https://your-dedicated-server.example.com/api"
self_service_url (String, Optional)
Redirect users to self-service enrollment if their card isn’t registered (Admin Panel → Security Keys → Workflows → Self-Service Actions).
"self_service_url": "https://panel.idmelon.com/self-service"
auto_logout (String, Optional)
Auto-logout after the given duration or after single use.
Allowed: one-time use, 5m, 60m, 2h, 4h, 6h, 8h
"auto_logout": "2h"
shortcut_list (JSON string, Optional)
Quick-access shortcuts inside the app.
Pretty:
{
\"shortcuts\": [
{ \"title\": \"My Apps\", \"url\": \"https://myapps.microsoft.com\", \"iconName\": \"microsoft.com\" },
{ \"title\": \"MS Teams\", \"url\": \"https://teams.microsoft.com\", \"iconName\": \"Teams\" }
]
}
The
\before the"is required.
open_url_after_login, open_url_after_logout (String, Optional)
Immediately after a user successfully signs in (or out), the app launches a specified application or web address.
"open_url_after_login": "https://..."
Don’t use these configurations if you have configured MSAL
It can be a URL scheme (to open a native app directly) or a regular URL (to open a website in the browser).
Examples for URL Scheme:
- Launch Microsoft Teams:
msteams:// - Launch Microsoft Excel:
ms-excel://
"open_url_after_login": "app-scheme://"
microsoft_sp_name (String, Optional)
Microsoft' service provider name in the IDmelon Admin Panel.
Default value: entra_id
"microsoft_sp_name": "entra_id"
default_sp_for_auto_login (String, Optional)
Set a service provider to log in automatically after the user signs in.
This configuration works for SSO login experience.
"default_sp_for_auto_login": "entra_id"
use_msal (Boolean, Optional)
If you plan to use Microsoft applications (such as Teams, Outlook, and other Office apps) on shared iPads, we recommend using MSAL.
This and the next configuration are required when enabling MSAL.
For detailed steps on configuring MSAL, please refer to Configuration for using MSAL.
"use_msal": true
azure_client_id (String, Optional)
Azure App Registration Client ID for MSAL.
"azure_client_id": "YOUR_AZURE_APP_CLIENT_ID"
Configure IDmelon Authenticator using Intune
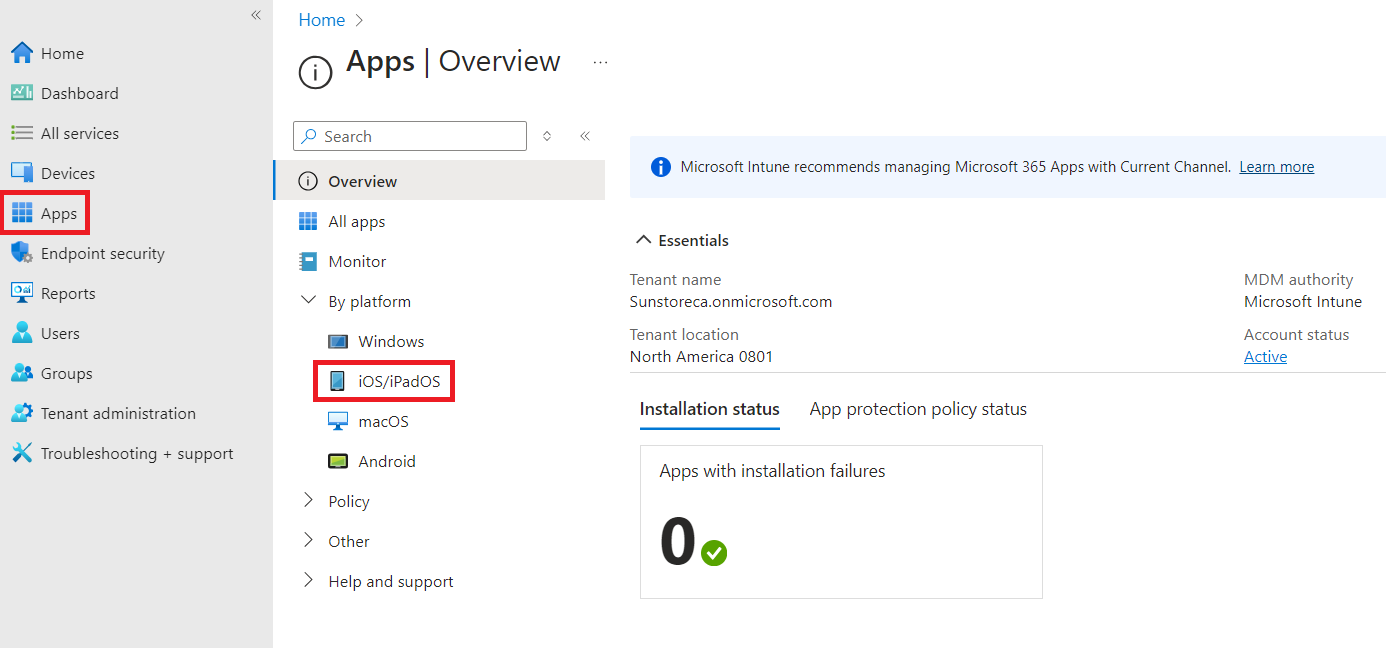
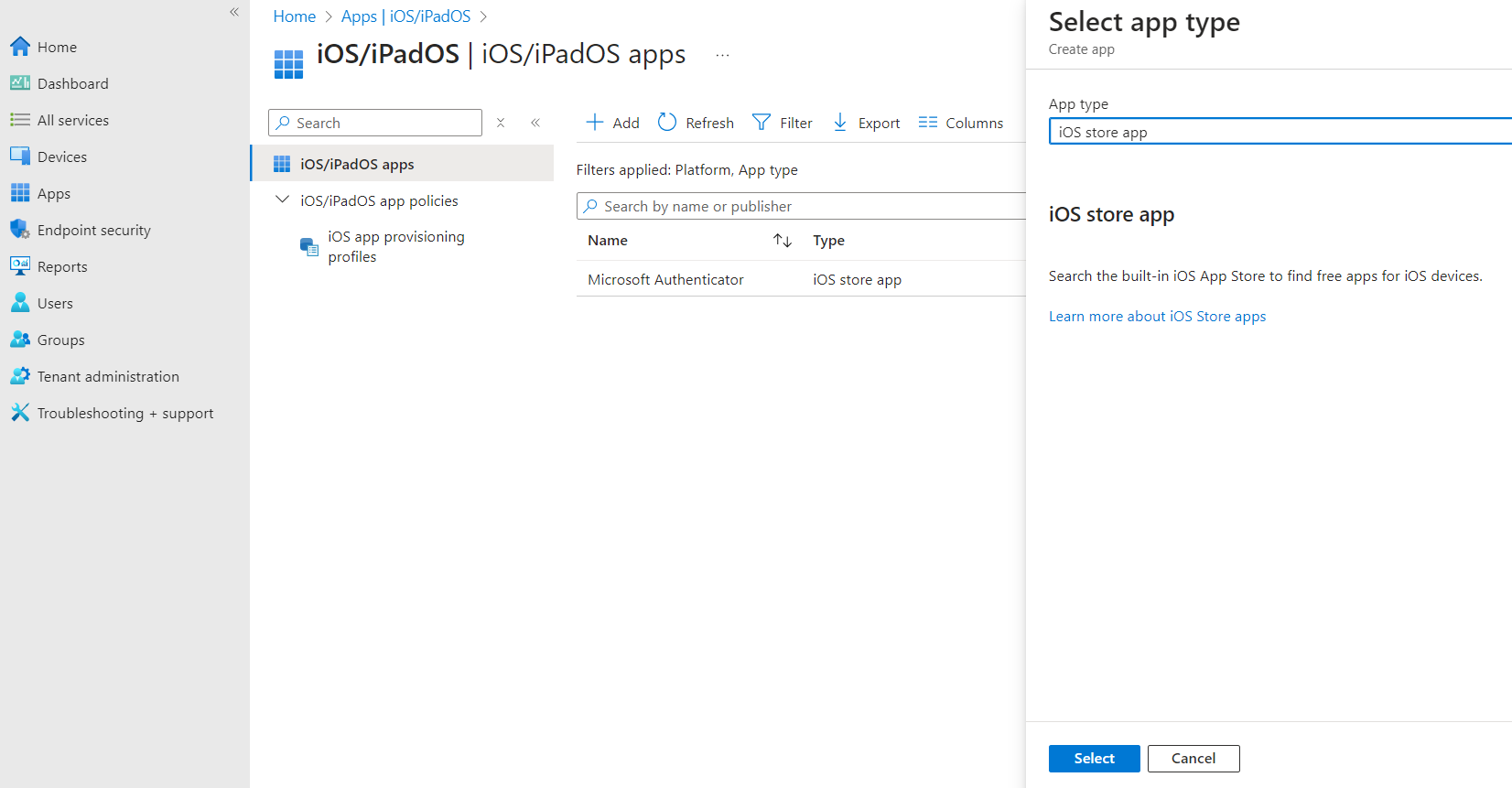
- Navigate to Apps > iOS/iPadOS.
- Click the Add button.
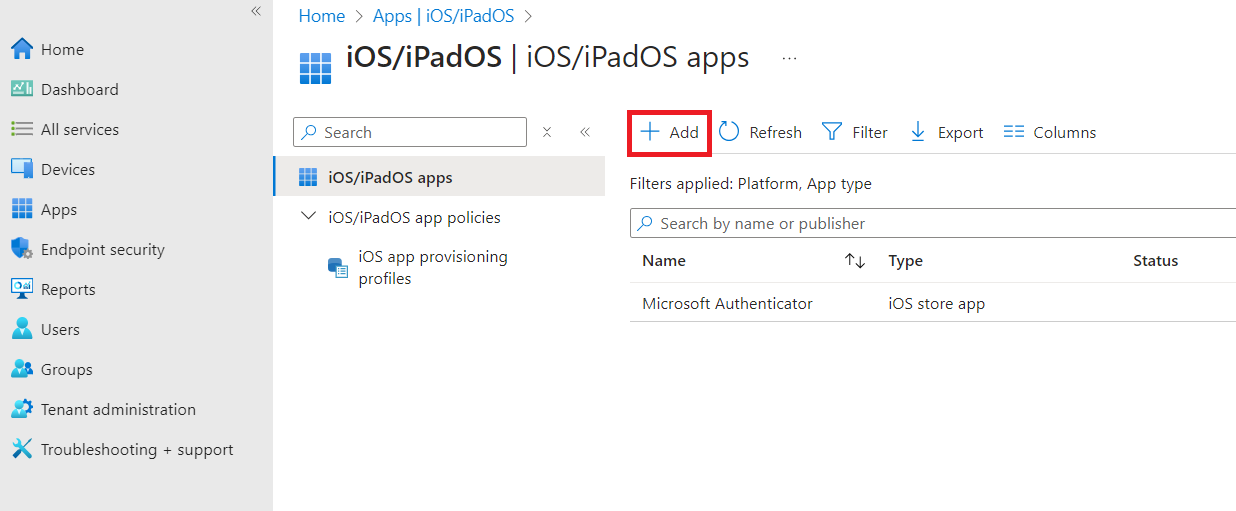
- Select iOS store app as the App type and click the Select button.
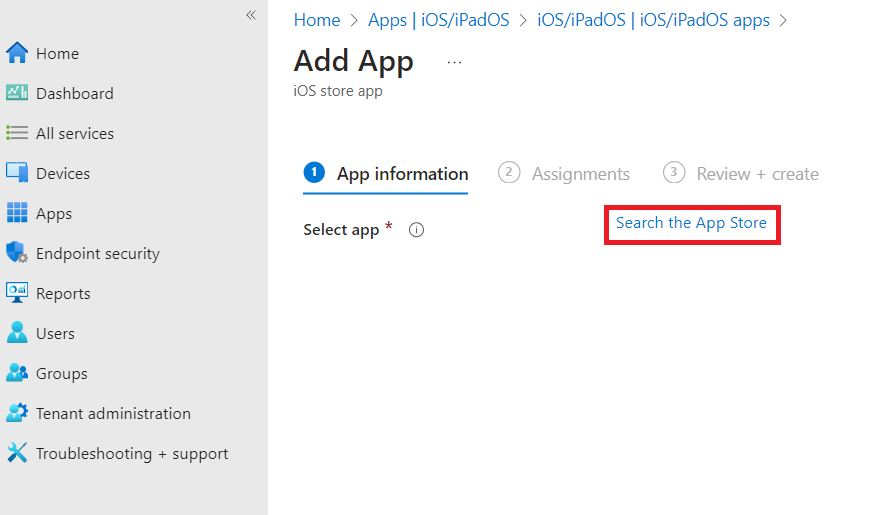
- Click the Search the App Store.
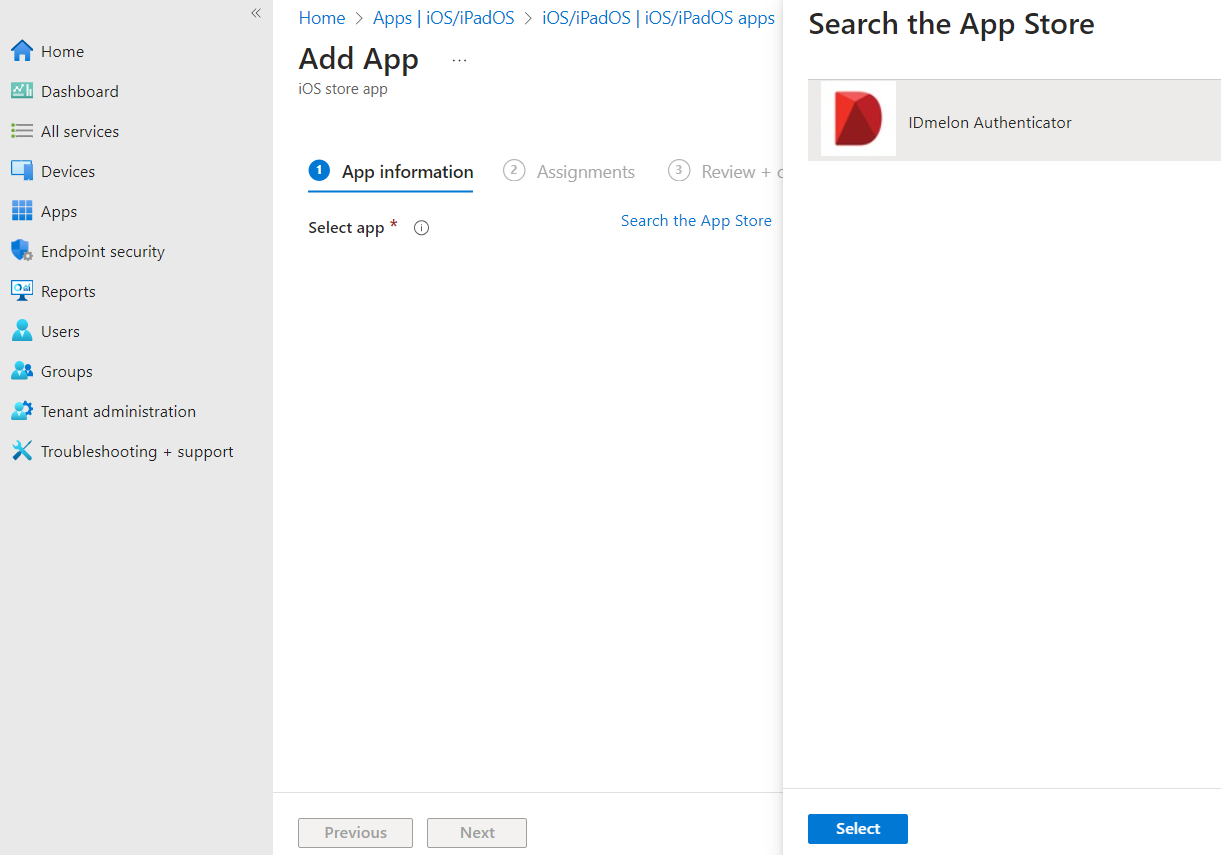
- Search for the IDmelon Authenticator app and click the Select button.
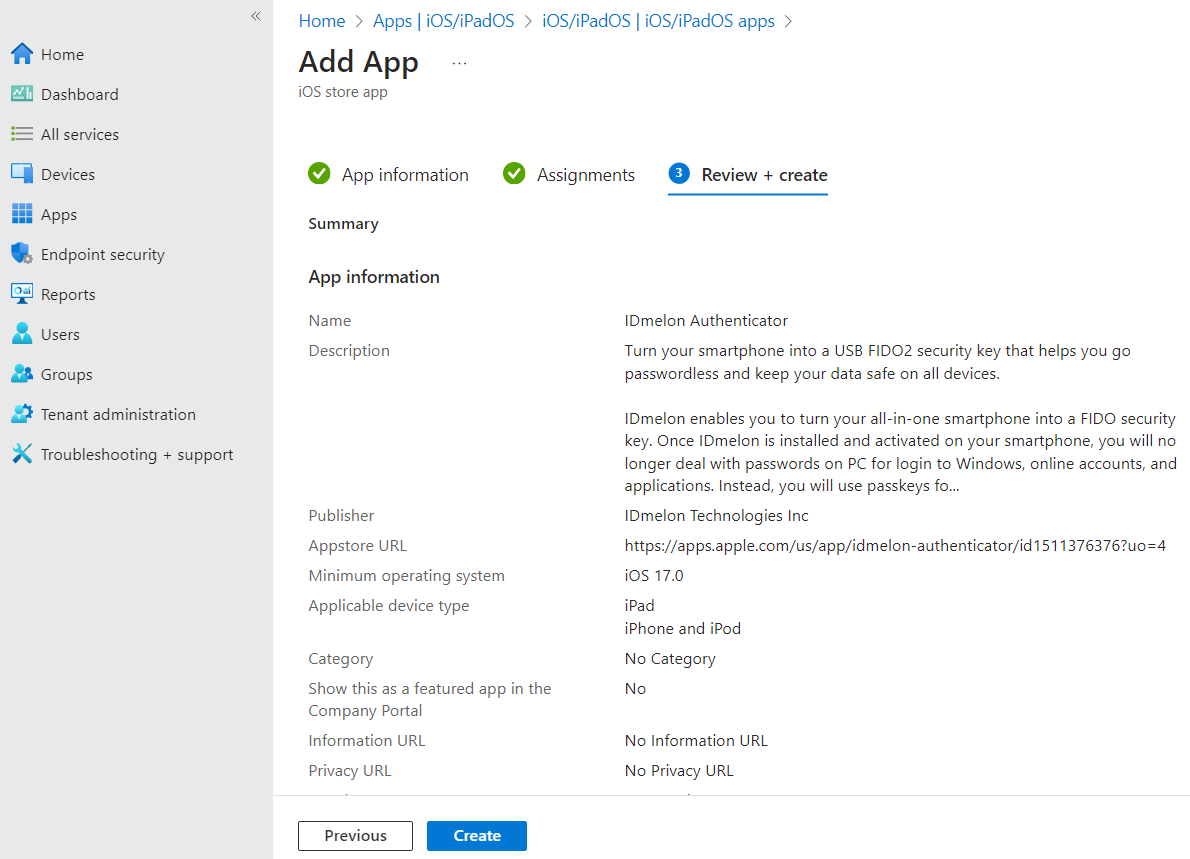
- Select iOS 17.0 as the Minimum operating system and click the Next button.
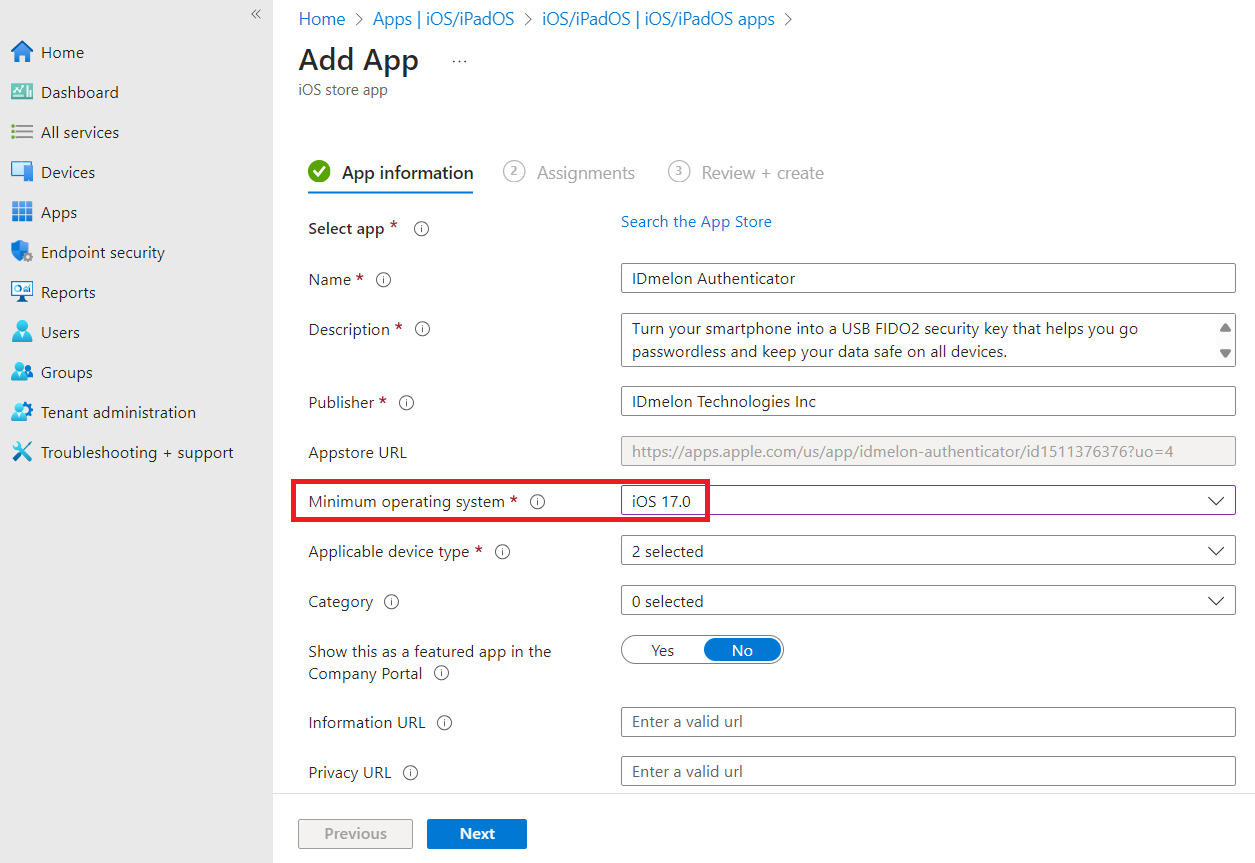
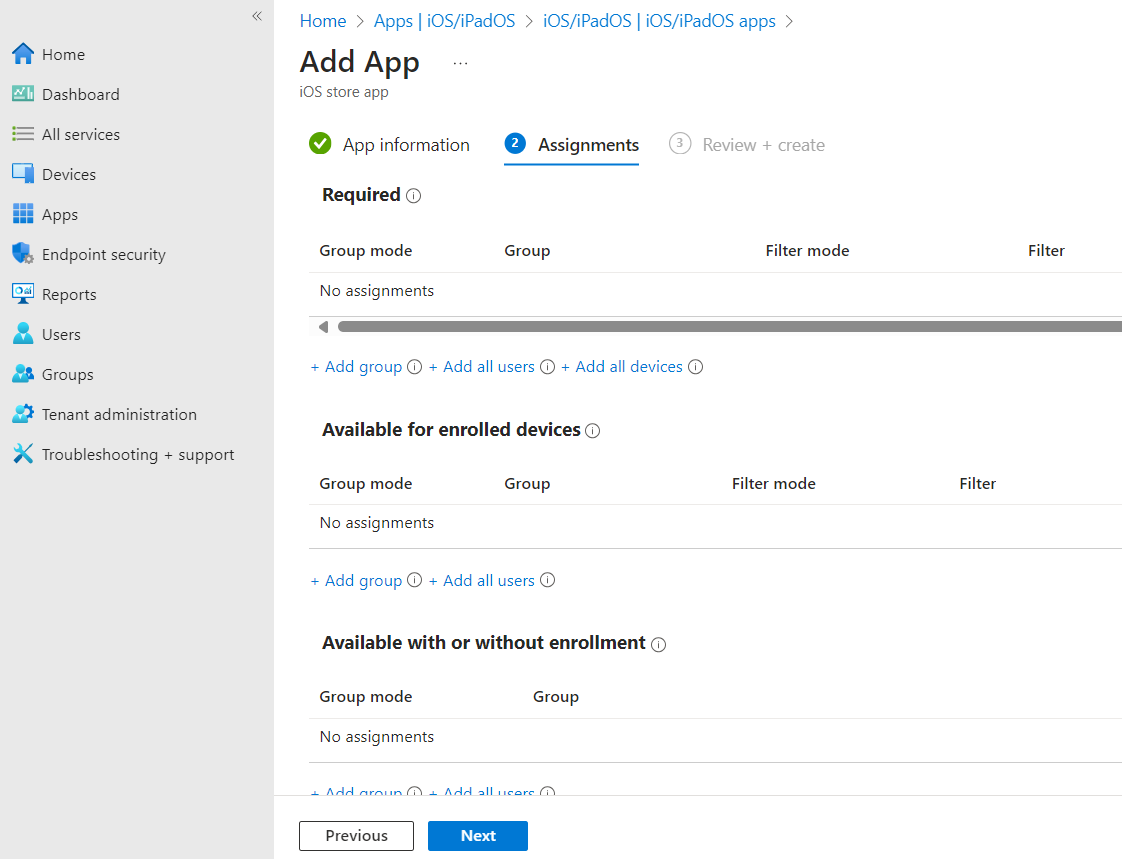
- Configure the Assignments tab according to your organization’s policies.
- Review the configurations you set and click the Create button.
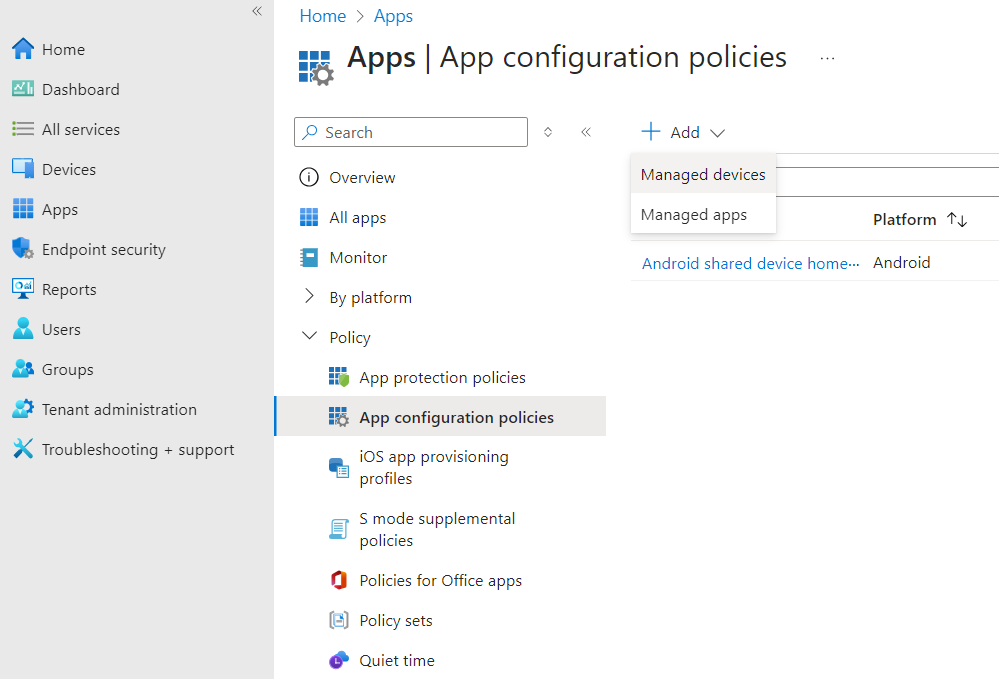
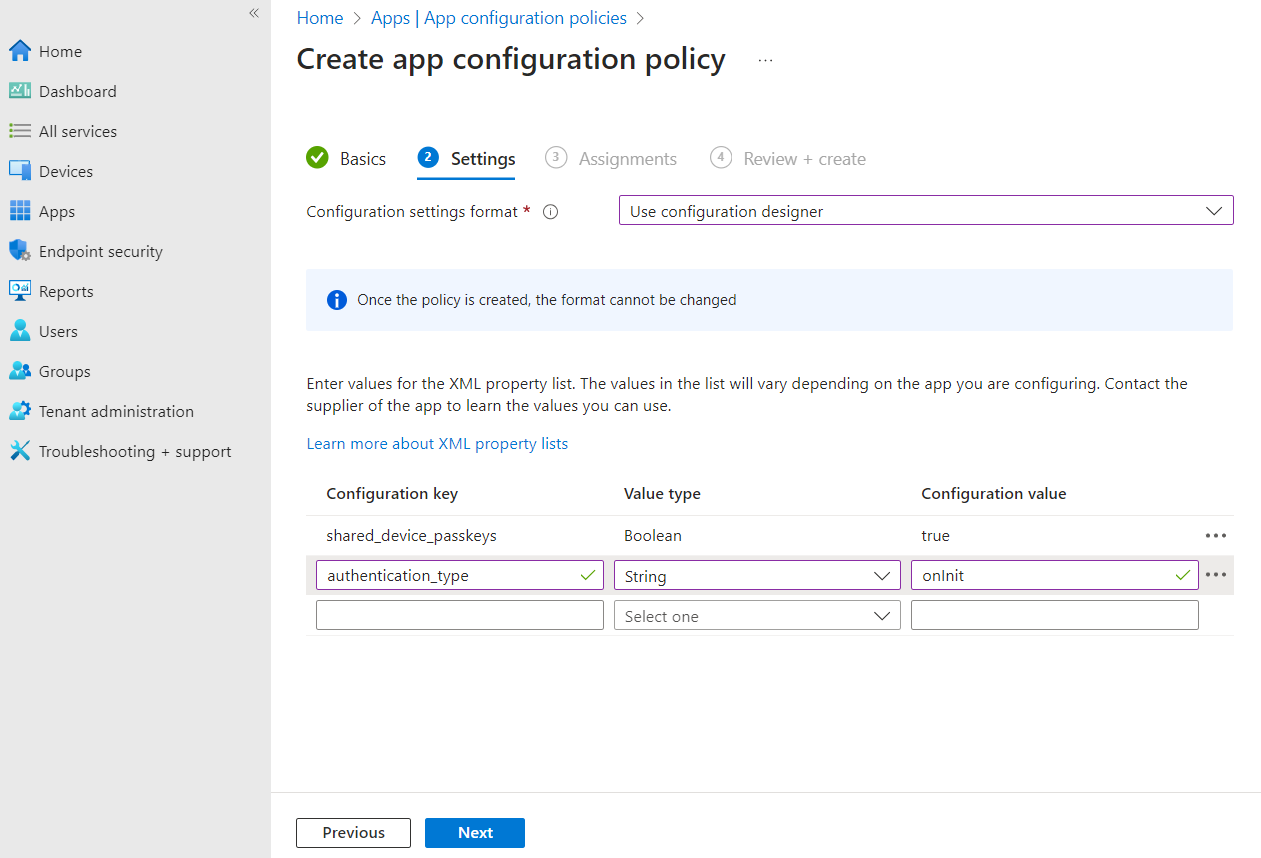
- Navigate to Apps > App configuration policies, click the + Add, and then Managed devices.
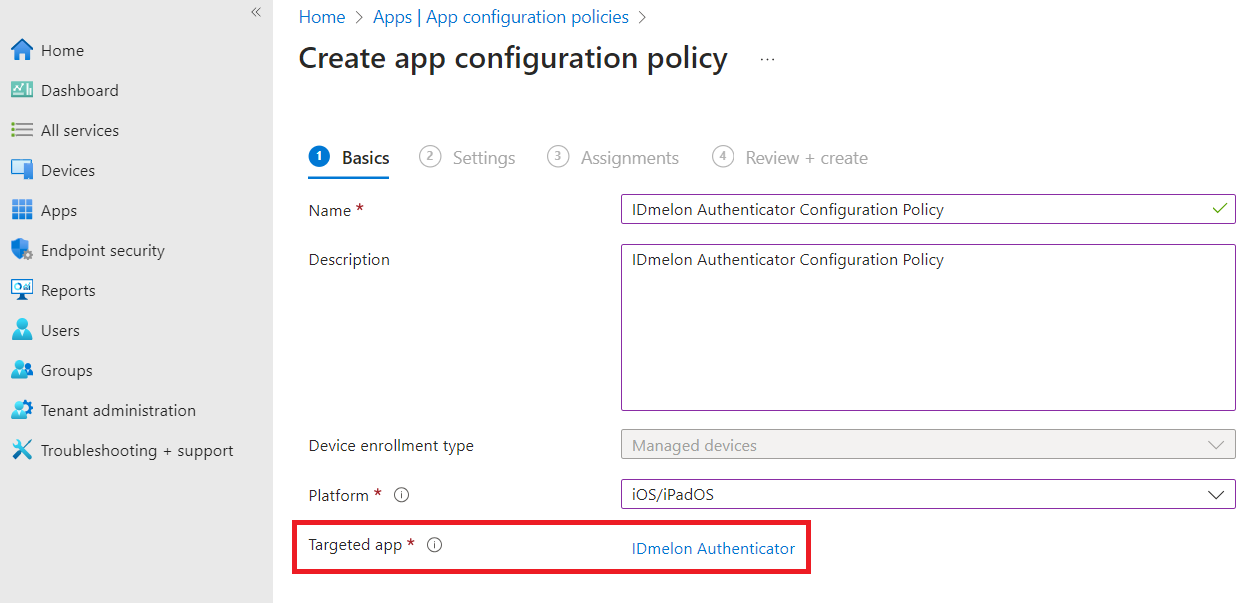
- Set a Name, select the iOS/iPadOS as the Platform, and IDmelon Authenticator as the Targeted app, then click the Next button.
- In the Settings tab, select the User configuration designer as the Configuration settings format, enter values for the configuration keys as explained in the Configuration Keys section above, and click the Next button.
Login Experience
When IDmelon Authenticator is configured in shared mode, users can walk in, tap their badge, and get the passkeys available to the device for authentication. Depending on the configuration, you can provide multiple user experiences.
Example 1: Basic configuration
Use the following configuration object when your MDM asks for app configuration (exact UI varies).
{
"shared_device_passkeys": true,
"authentication_type": "onInit",
"device_id": "{{deviceid}}",
"api_key": "YOUR_API_KEY"
}
Note: If you are using Microsoft products on the shared iPad (such as Microsoft Teams, Outlook, or Microsoft 365), we recommend configuring the Microsoft Enterprise SSO plug-in. This plug-in simplifies authentication and reduces repeated credential prompts (see Configuring the Microsoft Enterprise SSO plug-in).
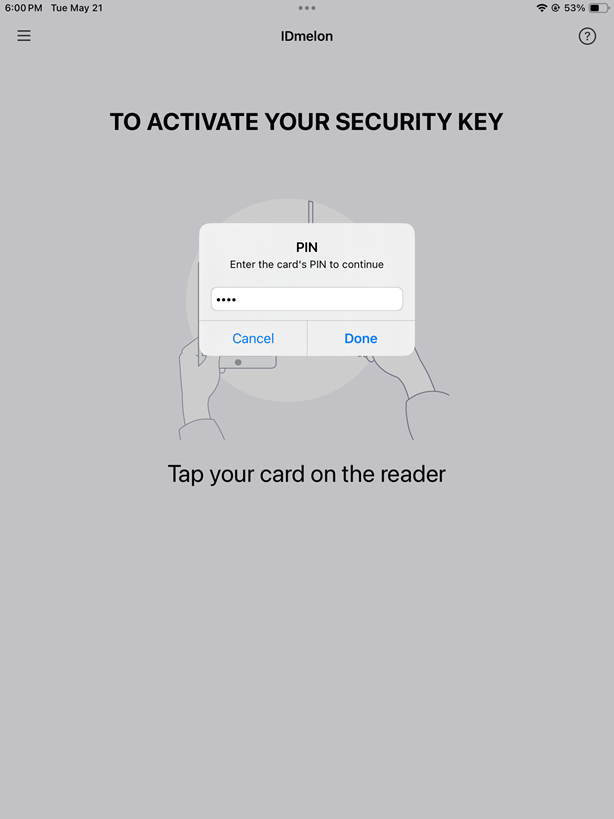
- Open the IDmelon Authenticator.
- Get close to the reader (or plug the keystroke reader) and tap your card on it.
- According to the Card Verification Method set in the IDmelon admin panel, if PIN is required, enter it. Otherwise, go to the next step.
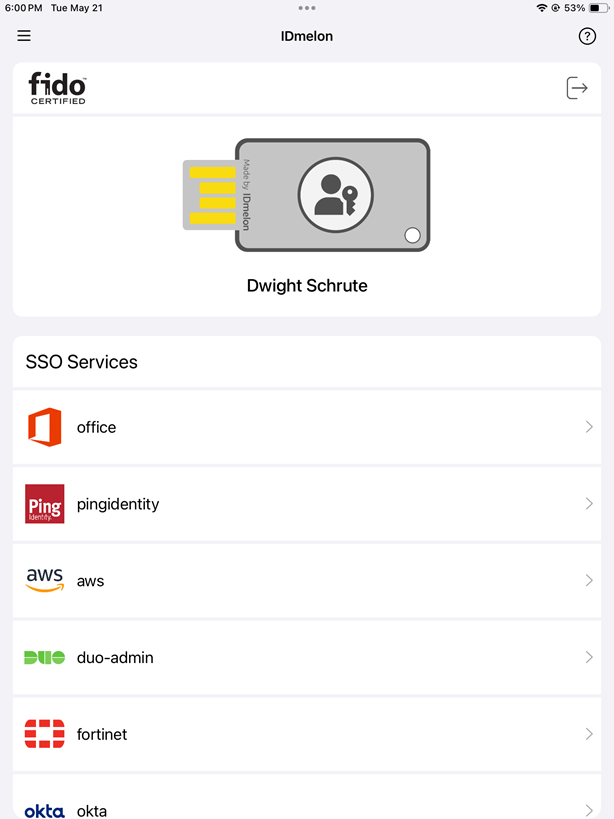
- In case of successful login, user information will be displayed. At this stage, move the app to the background.
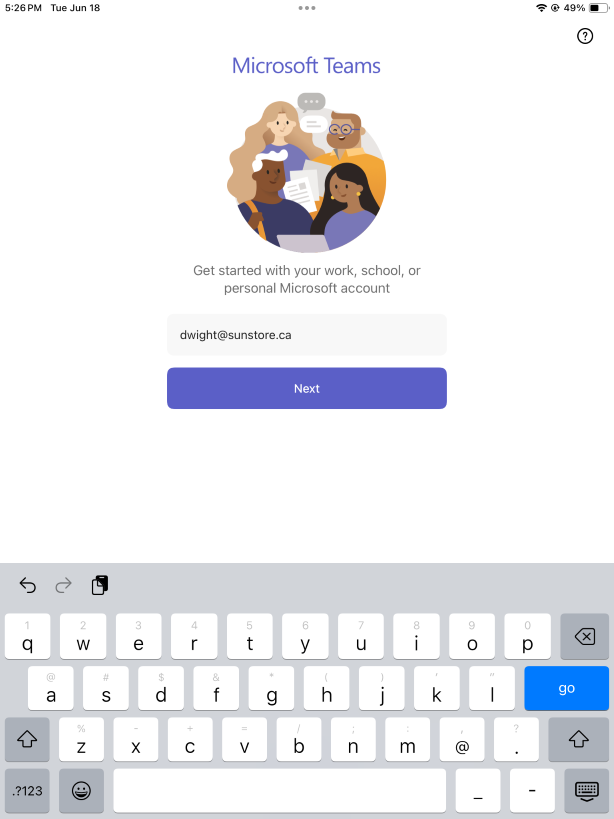
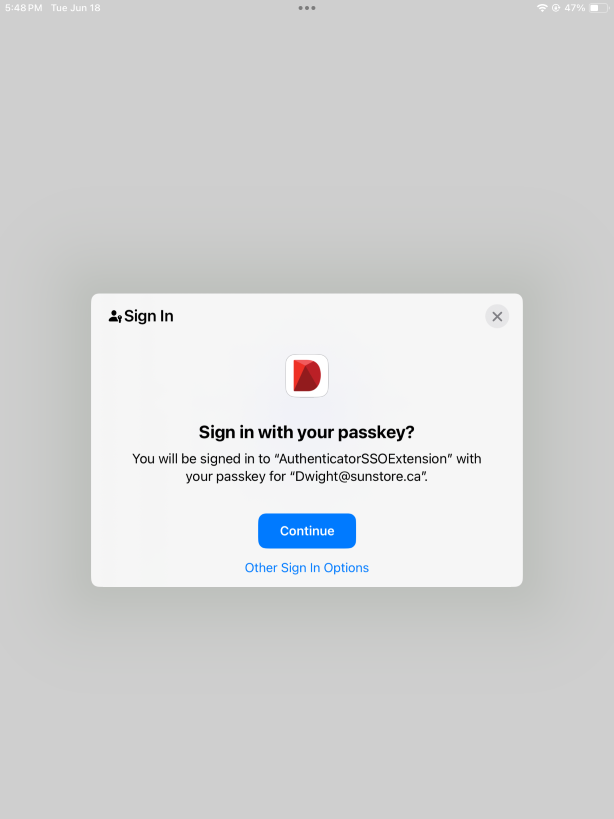
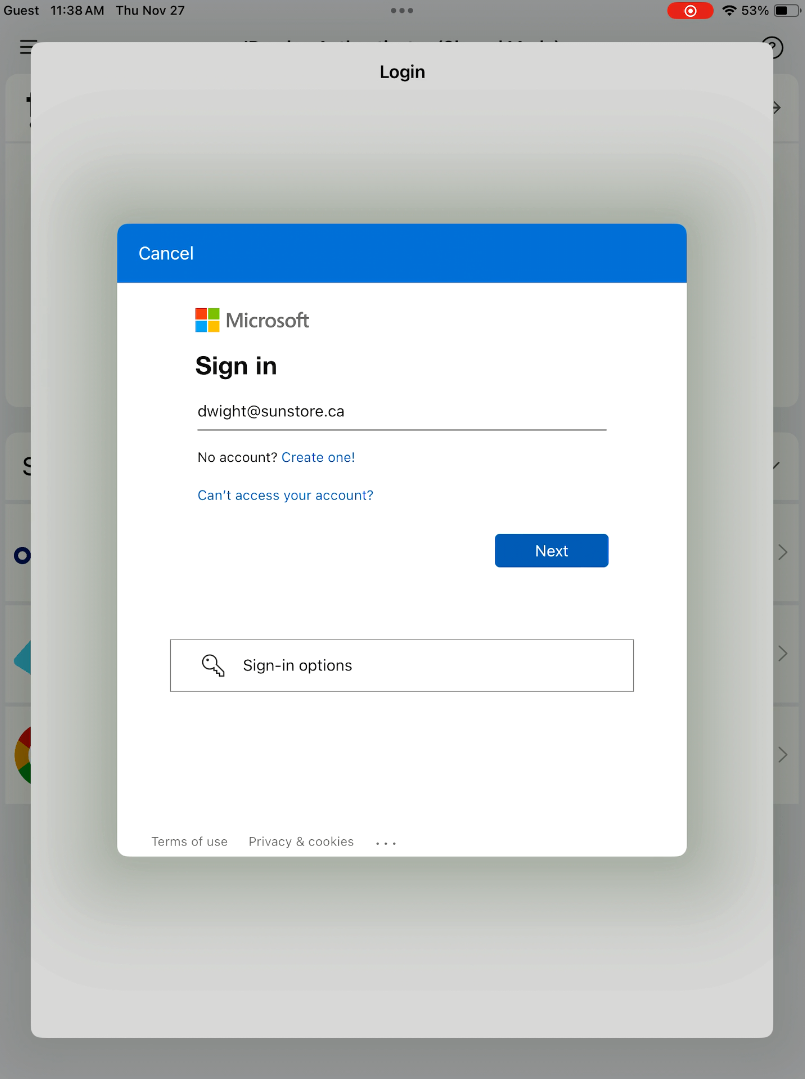
- Open the app you want to log in to using the passkey (e.g., MS Teams), tap the paste icon on the top left corner of the keyboard, and tap Next.
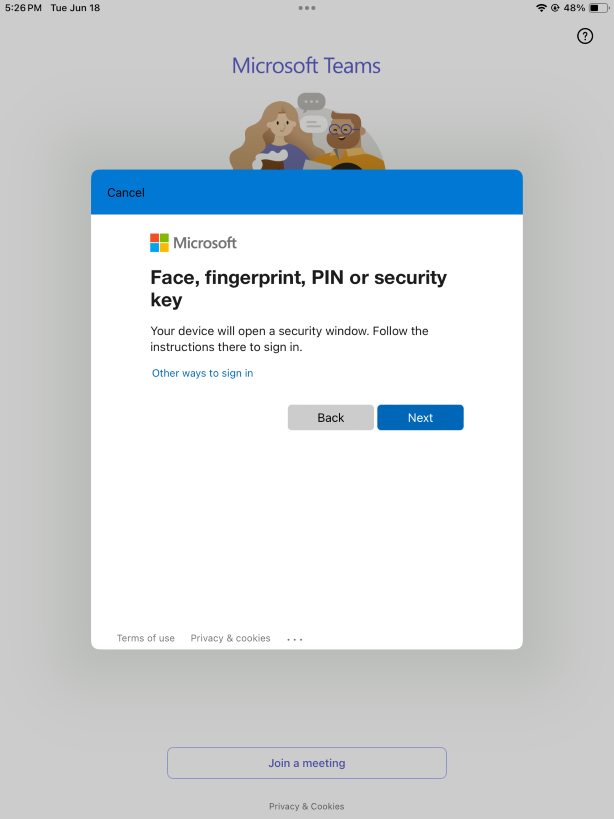
- Tap the Next.
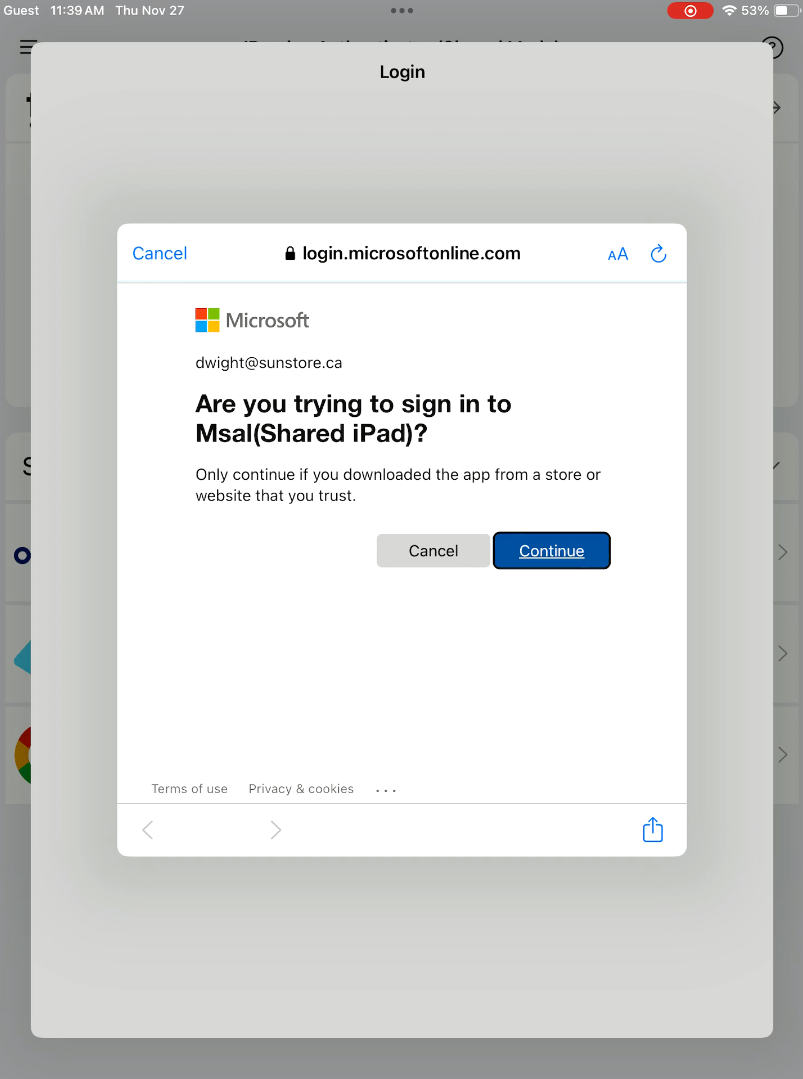
- Tap the Continue.
Example 2: SSO Login Experience
If you plan to use Microsoft applications (such as Teams, Outlook, and other Office apps) on shared iPads, we recommend using MSAL (see configuration guide).
Once MSAL has been configured, you can leverage the integrated authentication experience across Microsoft applications.
Use the following configuration object when your MDM asks for app configuration (exact UI varies).
{
"shared_device_passkeys": true,
"authentication_type": "onInit",
"device_id": "{{deviceid}}",
"api_key": "YOUR_API_KEY",
"use_msal": true,
"azure_client_id": "YOUR_AZURE_APP_CLIENT_ID"
}
Note: The
use_msalandazure_client_idconfiguration keys are required only when enabling the MSAL login experience.
Complete the user login steps (1-4) in the IDmelon Authenticator app according to the previous section.
After the user logs in, the MSAL prompt appears. Paste the user’s email, click Next, and then select Continue.
Move the app to the background.
Open any app you want to sign in to (for example, Teams).
Paste the email using the paste icon on the keyboard.
SSO Login for Non-Microsoft Service Providers
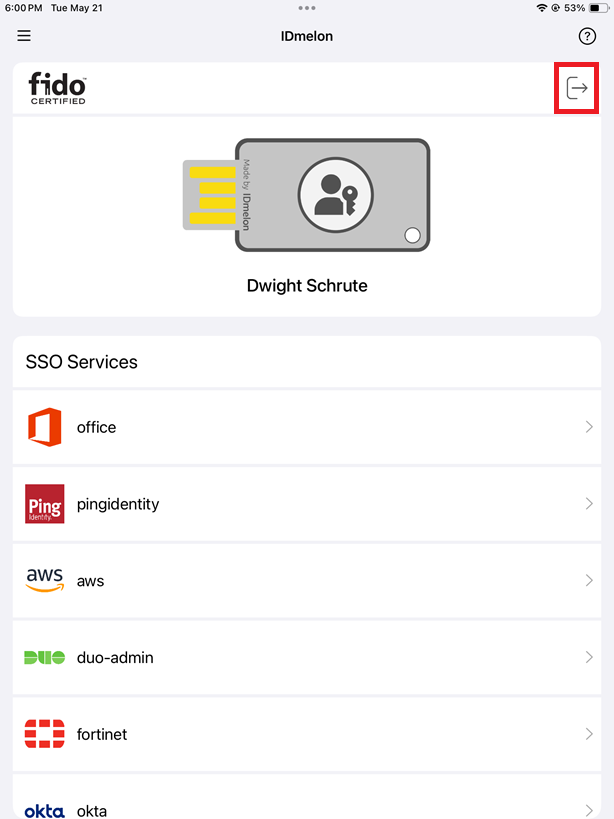
- After the user logs in, a list of available service providers is displayed in the app.
- By selecting any service provider, the device’s default browser opens and the user is automatically signed in to that provider.
Logout Experience
There are several ways to log out. One is manual, which you can see below. Another way is by managing the temporary session on iPad, which can streamline the logout experience. For more information, see Temporary Session Experience on Shared iPad.
Manual Logout from IDmelon Authenticator
This is a manual logout that, when MSAL is configured, can also trigger sign-out from Microsoft connected services as well.
- Open the app you logged into, and log out of the account.
- Open the IDmelon Authenticator and then tap the logout icon on the top right corner of the app. Your user information and existing passkeys will be deleted from the iPad.